Indice articolo
In an increasingly digital world, security has become an absolute priority. According to the IBM Cost of a Data Breach 2023 report, the global average cost of a data breach is around $4.45 million, with a 15% increase over the last three years. This highlights the growing need to adopt robust and comprehensive security measures through an integrated approach that covers the entire development process of our products.
This applies both at the application level (i.e within data) and at the infrastructure level (i.e. through AHD). This means that every phase of the development lifecycle is carefully monitored and protected by us using three distinct tools:
Let’s now analyse these tools in detail.
Dependabot

Dependabot is a tool developed by GitHub and designed to automate the update of software dependencies.
This allows us to have the following advantages:
- Increased Security: By automatically updating dependencies, we can quickly implement new releases containing security fixes, ensuring that our products are always protected against the latest threats
- Avoiding End of Support: We ensure that dependencies never reach the EoS status, thus preventing security and compatibility issues
- Quick Access to New Features: We can promptly take advantage of any new features introduced for dependencies, thereby contributing to performance improvements
- Reduction of Mean Time to Remediate (MTTR): Using an automated approach in combination with the continuous deployment mechanisms we already have allow us to reduce the average time needed to resolve security issues, even for customer installations
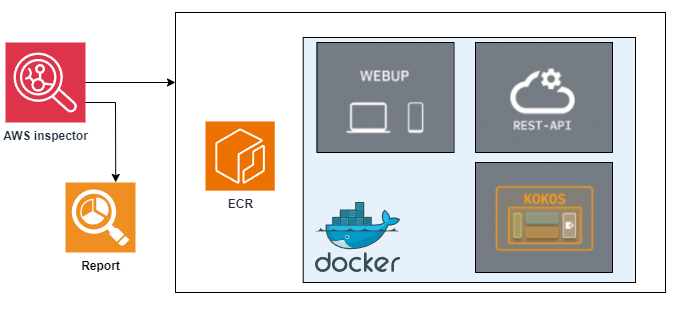
AWS Inspector

Inspector is an automated service from Amazon Web Services (AWS) that examines container images for vulnerabilities.
Its use for every single Docker image developed by smeup LAB offers us the following advantages:
- Automated Scanning: This significantly reduces the need to manually schedule and configure checks
- Reduction of MTTR: Like Dependabot, the combination with CD mechanisms allows us to reduce the MTTR for customer installations
- Continuous Scanning: Monitoring of resources does not only occur at their creation but continues throughout their lifecycle. This way, it is possible to assess the impact of introduced vulnerabilities resulting from changes made during the development process
- Detailed Report: When a vulnerability is detected, AWS Inspector creates a detailed report that includes: information about the vulnerability, recommendations for resolution, and a severity score
- Integration with AWS: AWS Inspector can be integrated with other AWS tools we already use during product development phases, all with minimal impact on performance, thus maintaining operational efficiency
OWASP ZAP

ZAP is an open-source tool that performs security tests for web applications developed by the Open Web Application Security Project (OWASP). Specifically, ZAP is used by us to identify real-time vulnerabilities related to the products webup.jsf and webup.js through:
- Automated Scanning: The tests performed by ZAP are fully automated
- Spidering (Crawling): ZAP can automatically explore web applications to identify all their resources
- Active and Passive Scanning: ZAP supports both passive scanning (monitoring traffic between the browser and the application without generating requests) and active scanning (sending custom requests to identify specific vulnerabilities)
- Support for Authentication: ZAP supports various authentication mechanisms, allowing us to test web applications under real conditions
- Plugins and Extensions: ZAP offers numerous plugins and extensions that enhance its capabilities, such as support for integrated reporting tools
Like Dependabot and AWS inspector, using ZAP in combination with CD mechanisms allows us to minimize the MTTR even for customer installations. Additionally, ZAP can be used to scan software directly on the customer’s installation, ensuring its security.
Workflow
Once we have discussed how adopting an integrated security approach that involves both the application and infrastructure aspects is fundamental for protecting our products against cyber threats we can now analyse how we use these tools.
In particular:
- First we configured dependabot in all the GitHub repositories through which we develop data in such a way that it can automatically manage and update our project dependencies. This tool is also involved in the CI/CD pipelines which are based on GitHub actions
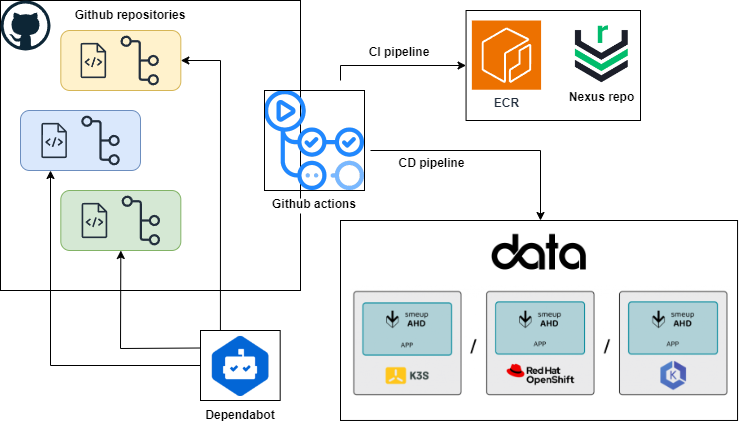
- Then we look for vulnerabilities in the container images produced through AWS inspector
- Finally rely on OWASP ZAP capabilities to promptly identify how our developments might affect our application in terms of vulnerabilities

These tools not only improve the overall security of our products but also optimize our development processes and allow us to implement continuous improvements.
